Filter News
Area of Research
News Topics
- (-) Climate Change (4)
- (-) Frontier (1)
- (-) Security (2)
- (-) Transportation (10)
- 3-D Printing/Advanced Manufacturing (10)
- Big Data (2)
- Bioenergy (2)
- Biology (1)
- Biomedical (1)
- Buildings (6)
- Clean Water (1)
- Computer Science (4)
- Coronavirus (4)
- Critical Materials (1)
- Cybersecurity (2)
- Decarbonization (8)
- Energy Storage (11)
- Environment (8)
- Exascale Computing (1)
- Grid (6)
- High-Performance Computing (3)
- Materials (3)
- Materials Science (1)
- Mathematics (1)
- Mercury (1)
- Microscopy (1)
- National Security (1)
- Net Zero (1)
- Neutron Science (5)
- Simulation (1)
- Summit (1)
- Sustainable Energy (6)
Media Contacts

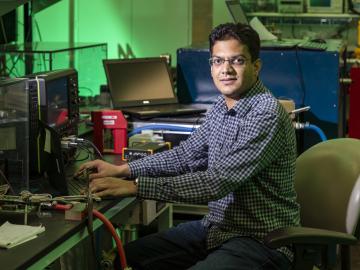
An international problem like climate change needs solutions that cross boundaries, both on maps and among disciplines. Oak Ridge National Laboratory computational scientist Deeksha Rastogi embodies that approach.

Ross Wang has been intent on resolving traffic jams since he rode a city bus every day through 40 minutes of traffic to get to his elementary school. That daily journey left an impression that would shape his career.

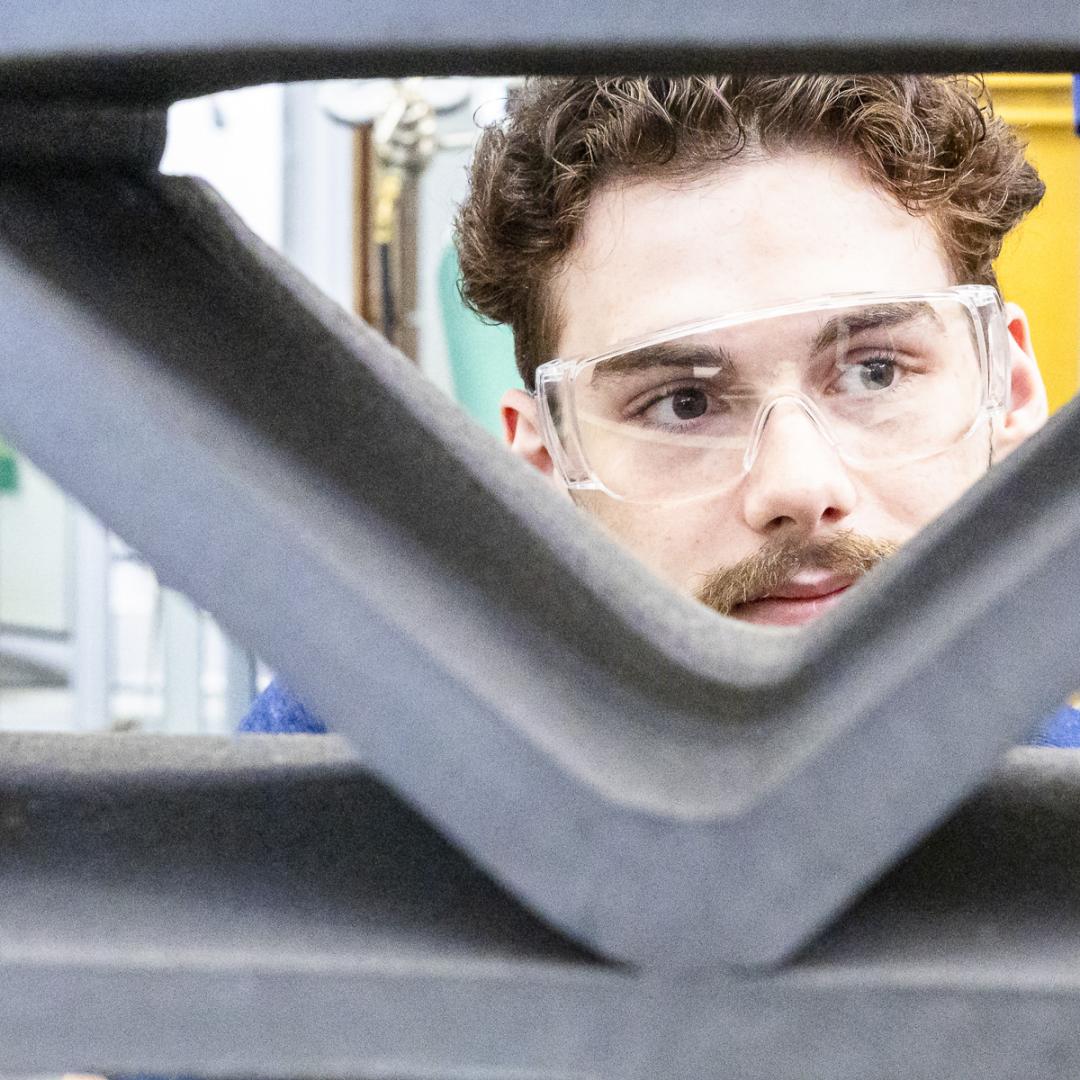
For a researcher who started out in mechanical engineering with a focus on engine combustion, Martin Wissink has learned a lot about neutrons on the job

In Hong Wang’s world, nothing is beyond control. Before joining Oak Ridge National Laboratory as a senior distinguished researcher in transportation systems, he spent more than three decades studying the control of complex industrial systems in the United Kingdom.
Galigekere is principal investigator for the breakthrough work in fast, wireless charging of electric vehicles being performed at the National Transportation Research Center at Oak Ridge National Laboratory.
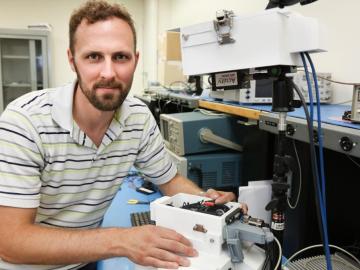
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.