Filter News
Area of Research
- (-) Clean Energy (41)
- (-) Supercomputing (62)
- Advanced Manufacturing (3)
- Biological Systems (1)
- Biology and Environment (41)
- Climate and Environmental Systems (1)
- Computational Biology (2)
- Computational Engineering (2)
- Computer Science (3)
- Fusion and Fission (10)
- Fusion Energy (7)
- Isotope Development and Production (1)
- Isotopes (27)
- Materials (84)
- Materials for Computing (10)
- Mathematics (1)
- National Security (23)
- Neutron Science (34)
- Nuclear Science and Technology (22)
- Nuclear Systems Modeling, Simulation and Validation (1)
- Quantum information Science (9)
News Topics
- (-) Advanced Reactors (7)
- (-) Biomedical (22)
- (-) Clean Water (8)
- (-) Cybersecurity (14)
- (-) Isotopes (1)
- (-) Mercury (3)
- (-) Microscopy (14)
- (-) Physics (7)
- (-) Quantum Science (25)
- (-) Space Exploration (6)
- 3-D Printing/Advanced Manufacturing (80)
- Artificial Intelligence (41)
- Big Data (24)
- Bioenergy (29)
- Biology (19)
- Biotechnology (6)
- Buildings (37)
- Chemical Sciences (16)
- Climate Change (35)
- Composites (17)
- Computer Science (107)
- Coronavirus (25)
- Critical Materials (12)
- Decarbonization (35)
- Energy Storage (75)
- Environment (68)
- Exascale Computing (23)
- Fossil Energy (2)
- Frontier (28)
- Fusion (2)
- Grid (42)
- High-Performance Computing (39)
- Hydropower (2)
- Machine Learning (19)
- Materials (45)
- Materials Science (40)
- Mathematics (3)
- Microelectronics (1)
- Molten Salt (1)
- Nanotechnology (15)
- National Security (11)
- Net Zero (4)
- Neutron Science (20)
- Nuclear Energy (11)
- Partnerships (12)
- Polymers (13)
- Quantum Computing (19)
- Renewable Energy (1)
- Security (9)
- Simulation (16)
- Software (1)
- Statistics (1)
- Summit (43)
- Sustainable Energy (71)
- Transformational Challenge Reactor (3)
- Transportation (69)
Media Contacts
By analyzing a pattern formed by the intersection of two beams of light, researchers can capture elusive details regarding the behavior of mysterious phenomena such as gravitational waves. Creating and precisely measuring these interference patterns would not be possible without instruments called interferometers.

Biologists from Oak Ridge National Laboratory and the Smithsonian Environmental Research Center have confirmed that microorganisms called methanogens can transform mercury into the neurotoxin methylmercury with varying efficiency across species.
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.
Scientists at the Department of Energy’s Oak Ridge National Laboratory are the first to successfully simulate an atomic nucleus using a quantum computer. The results, published in Physical Review Letters, demonstrate the ability of quantum systems to compute nuclear ph...

Last November a team of students and educators from Robertsville Middle School in Oak Ridge and scientists from Oak Ridge National Laboratory submitted a proposal to NASA for their Cube Satellite Launch Initiative in hopes of sending a student-designed nanosatellite named RamSat into...

A novel method developed at Oak Ridge National Laboratory creates supertough renewable plastic with improved manufacturability. Working with polylactic acid, a biobased plastic often used in packaging, textiles, biomedical implants and 3D printing, the research team added tiny amo...
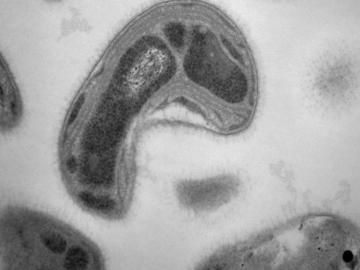
A team led by the Department of Energy’s Oak Ridge National Laboratory has identified a novel microbial process that can break down toxic methylmercury in the environment, a fundamental scientific discovery that could potentially reduce mercury toxicity levels and sup...

Virginia-based Lenvio Inc. has exclusively licensed a cyber security technology from the Department of Energy’s Oak Ridge National Laboratory that can quickly detect malicious behavior in software not previously identified as a threat.