Filter News
Area of Research
News Topics
- (-) Net Zero (2)
- (-) Security (2)
- 3-D Printing/Advanced Manufacturing (10)
- Advanced Reactors (1)
- Big Data (2)
- Bioenergy (12)
- Biology (18)
- Biomedical (5)
- Biotechnology (2)
- Buildings (6)
- Chemical Sciences (3)
- Clean Water (5)
- Climate Change (8)
- Composites (1)
- Computer Science (3)
- Coronavirus (6)
- Critical Materials (1)
- Cybersecurity (2)
- Decarbonization (12)
- Energy Storage (12)
- Environment (29)
- Exascale Computing (1)
- Fusion (1)
- Grid (6)
- High-Performance Computing (5)
- Hydropower (2)
- Machine Learning (1)
- Materials (3)
- Materials Science (3)
- Mathematics (3)
- Mercury (4)
- Microscopy (5)
- National Security (1)
- Neutron Science (1)
- Nuclear Energy (3)
- Physics (2)
- Polymers (1)
- Simulation (3)
- Summit (2)
- Sustainable Energy (12)
- Transportation (10)
Media Contacts

Carl Dukes’ career as an adept communicator got off to a slow start: He was about 5 years old when he spoke for the first time. “I’ve been making up for lost time ever since,” joked Dukes, a technical professional at the Department of Energy’s Oak Ridge National Laboratory.

Matthew Craig grew up eagerly exploring the forest patches and knee-high waterfalls just beyond his backyard in central Illinois’ corn belt. Today, that natural curiosity and the expertise he’s cultivated in biogeochemistry and ecology are focused on how carbon cycles in and out of soils, a process that can have tremendous impact on the Earth’s climate.

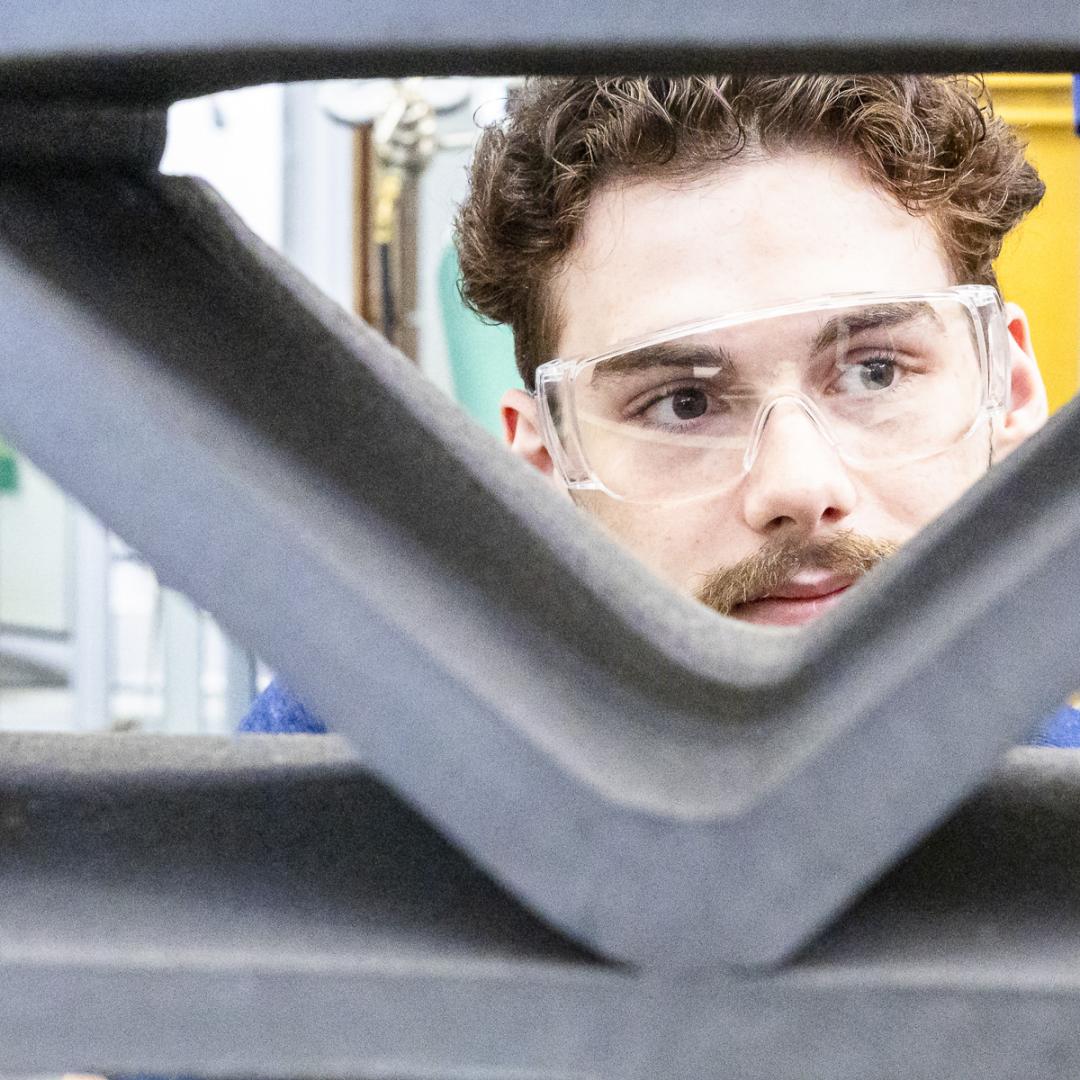
What’s getting Jim Szybist fired up these days? It’s the opportunity to apply his years of alternative fuel combustion and thermodynamics research to the challenge of cleaning up the hard-to-decarbonize, heavy-duty mobility sector — from airplanes to locomotives to ships and massive farm combines.
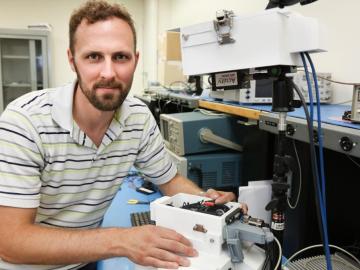
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.