Filter News
Area of Research
News Topics
- (-) Biomedical (2)
- (-) Cybersecurity (2)
- (-) Materials Science (1)
- 3-D Printing/Advanced Manufacturing (4)
- Artificial Intelligence (6)
- Bioenergy (3)
- Biology (3)
- Biotechnology (2)
- Buildings (3)
- Chemical Sciences (3)
- Climate Change (3)
- Composites (1)
- Computer Science (8)
- Coronavirus (2)
- Critical Materials (1)
- Decarbonization (7)
- Energy Storage (9)
- Environment (2)
- Exascale Computing (4)
- Frontier (5)
- Grid (4)
- High-Performance Computing (7)
- Machine Learning (2)
- Materials (8)
- Microscopy (2)
- Nanotechnology (1)
- National Security (3)
- Net Zero (1)
- Neutron Science (1)
- Nuclear Energy (1)
- Partnerships (4)
- Physics (1)
- Quantum Science (2)
- Renewable Energy (1)
- Security (4)
- Simulation (2)
- Summit (2)
- Sustainable Energy (1)
- Transportation (6)
Media Contacts

Four scientists affiliated with ORNL were named Battelle Distinguished Inventors during the lab’s annual Innovation Awards on Dec. 1 in recognition of being granted 14 or more United States patents.
Scientists at ORNL used their expertise in quantum biology, artificial intelligence and bioengineering to improve how CRISPR Cas9 genome editing tools work on organisms like microbes that can be modified to produce renewable fuels and chemicals.

Carl Dukes’ career as an adept communicator got off to a slow start: He was about 5 years old when he spoke for the first time. “I’ve been making up for lost time ever since,” joked Dukes, a technical professional at the Department of Energy’s Oak Ridge National Laboratory.

Scientist-inventors from ORNL will present seven new technologies during the Technology Innovation Showcase on Friday, July 14, from 8 a.m.–4 p.m. at the Joint Institute for Computational Sciences on ORNL’s campus.
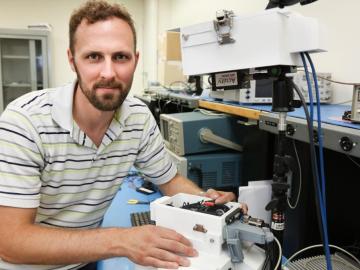
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.