
Filter News
Area of Research
News Topics
- (-) Artificial Intelligence (2)
- (-) Cybersecurity (3)
- (-) Microscopy (1)
- (-) Nanotechnology (1)
- 3-D Printing/Advanced Manufacturing (7)
- Advanced Reactors (1)
- Big Data (1)
- Bioenergy (3)
- Biology (1)
- Biomedical (1)
- Clean Water (1)
- Climate Change (1)
- Computer Science (4)
- Coronavirus (5)
- Energy Storage (7)
- Environment (4)
- Grid (5)
- Machine Learning (1)
- Materials Science (5)
- Mathematics (1)
- Neutron Science (1)
- Nuclear Energy (1)
- Polymers (1)
- Quantum Science (1)
- Security (3)
- Space Exploration (1)
- Summit (1)
- Sustainable Energy (3)
- Transportation (6)
Media Contacts

The University of Texas at San Antonio (UTSA) has formally launched the Cybersecurity Manufacturing Innovation Institute (CyManII), a $111 million public-private partnership.
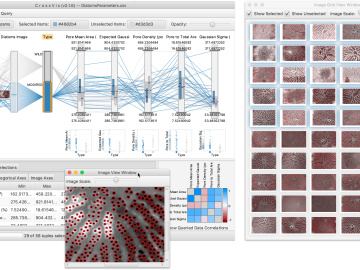
From materials science and earth system modeling to quantum information science and cybersecurity, experts in many fields run simulations and conduct experiments to collect the abundance of data necessary for scientific progress.
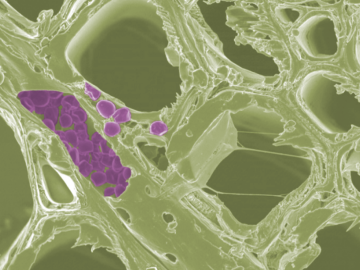
Scientists at the Department of Energy’s Oak Ridge National Laboratory have developed a new method to peer deep into the nanostructure of biomaterials without damaging the sample. This novel technique can confirm structural features in starch, a carbohydrate important in biofuel production.

Each year, approximately 6 billion gallons of fuel are wasted as vehicles wait at stop lights or sit in dense traffic with engines idling, according to US Department of Energy estimates.

A typhoon strikes an island in the Pacific Ocean, downing power lines and cell towers. An earthquake hits a remote mountainous region, destroying structures and leaving no communication infrastructure behind.
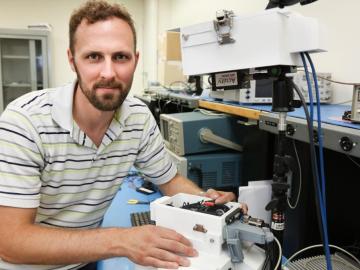
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.


