
Filter News
Area of Research
News Topics
- (-) Artificial Intelligence (1)
- (-) Biomedical (1)
- (-) Computer Science (3)
- (-) Polymers (1)
- (-) Security (1)
- 3-D Printing/Advanced Manufacturing (5)
- Bioenergy (3)
- Biology (1)
- Biotechnology (1)
- Clean Water (1)
- Climate Change (1)
- Cybersecurity (1)
- Energy Storage (3)
- Environment (4)
- Grid (3)
- Mercury (1)
- Nanotechnology (1)
- Nuclear Energy (1)
- Space Exploration (1)
- Sustainable Energy (1)
- Transportation (4)
Media Contacts
Students often participate in internships and receive formal training in their chosen career fields during college, but some pursue professional development opportunities even earlier.
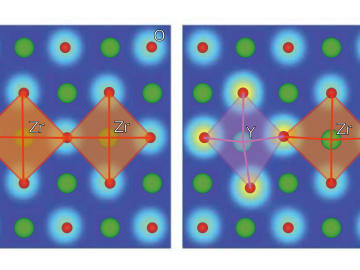
Ionic conduction involves the movement of ions from one location to another inside a material. The ions travel through point defects, which are irregularities in the otherwise consistent arrangement of atoms known as the crystal lattice. This sometimes sluggish process can limit the performance and efficiency of fuel cells, batteries, and other energy storage technologies.
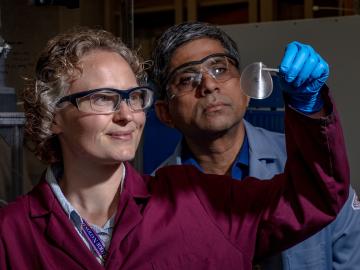
Scientists at the Department of Energy’s Oak Ridge National Laboratory are working to understand both the complex nature of uranium and the various oxide forms it can take during processing steps that might occur throughout the nuclear fuel cycle.
![Coexpression_hi-res_image[1].jpg Coexpression_hi-res_image[1].jpg](/sites/default/files/styles/list_page_thumbnail/public/Coexpression_hi-res_image%5B1%5D_0.jpg?itok=OnLe-krT)
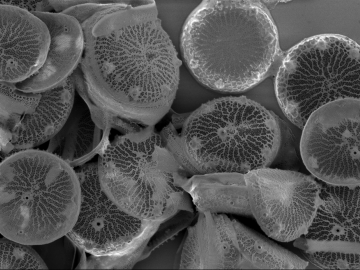
While studying the genes in poplar trees that control callus formation, scientists at Oak Ridge National Laboratory have uncovered genetic networks at the root of tumor formation in several human cancers.
Oak Ridge National Laboratory scientists have developed a crucial component for a new kind of low-cost stationary battery system utilizing common materials and designed for grid-scale electricity storage. Large, economical electricity storage systems can benefit the nation’s grid ...
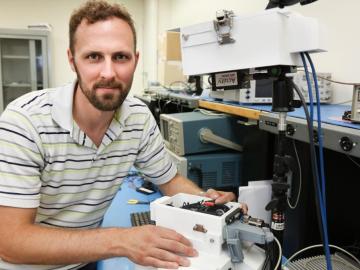
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.


