Filter News
Area of Research
News Topics
- (-) Security (10)
- (-) Transformational Challenge Reactor (3)
- 3-D Printing/Advanced Manufacturing (35)
- Advanced Reactors (8)
- Artificial Intelligence (45)
- Big Data (21)
- Bioenergy (49)
- Biology (57)
- Biomedical (28)
- Biotechnology (10)
- Buildings (17)
- Chemical Sciences (21)
- Clean Water (14)
- Climate Change (47)
- Composites (6)
- Computer Science (80)
- Coronavirus (17)
- Critical Materials (1)
- Cybersecurity (14)
- Decarbonization (43)
- Education (1)
- Emergency (2)
- Energy Storage (28)
- Environment (100)
- Exascale Computing (24)
- Fossil Energy (4)
- Frontier (23)
- Fusion (28)
- Grid (23)
- High-Performance Computing (42)
- Hydropower (5)
- Isotopes (26)
- ITER (2)
- Machine Learning (21)
- Materials (40)
- Materials Science (43)
- Mathematics (5)
- Mercury (7)
- Microelectronics (2)
- Microscopy (20)
- Molten Salt (1)
- Nanotechnology (16)
- National Security (33)
- Net Zero (8)
- Neutron Science (47)
- Nuclear Energy (52)
- Partnerships (15)
- Physics (27)
- Polymers (8)
- Quantum Computing (19)
- Quantum Science (29)
- Renewable Energy (1)
- Simulation (29)
- Software (1)
- Space Exploration (12)
- Summit (30)
- Sustainable Energy (43)
- Transportation (27)
Media Contacts

A typhoon strikes an island in the Pacific Ocean, downing power lines and cell towers. An earthquake hits a remote mountainous region, destroying structures and leaving no communication infrastructure behind.

As technology continues to evolve, cybersecurity threats do as well. To better safeguard digital information, a team of researchers at the US Department of Energy’s (DOE’s) Oak Ridge National Laboratory (ORNL) has developed Akatosh, a security analysis tool that works in conjunctio...
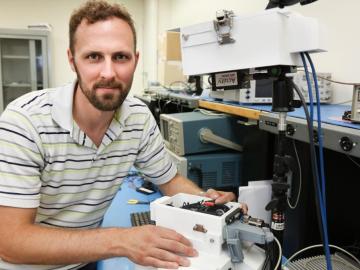
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.

