Filter News
Area of Research
- (-) Biology and Environment (18)
- (-) Clean Energy (44)
- (-) National Security (15)
- Advanced Manufacturing (2)
- Computer Science (1)
- Fusion and Fission (3)
- Isotopes (13)
- Materials (31)
- Materials for Computing (5)
- Neutron Science (46)
- Nuclear Science and Technology (4)
- Quantum information Science (1)
- Supercomputing (23)
News Type
News Topics
- (-) Clean Water (6)
- (-) Cybersecurity (16)
- (-) Exascale Computing (3)
- (-) Isotopes (2)
- (-) Neutron Science (12)
- (-) Sustainable Energy (38)
- 3-D Printing/Advanced Manufacturing (41)
- Advanced Reactors (4)
- Artificial Intelligence (12)
- Big Data (4)
- Bioenergy (32)
- Biology (36)
- Biomedical (11)
- Biotechnology (8)
- Buildings (14)
- Chemical Sciences (14)
- Climate Change (22)
- Composites (7)
- Computer Science (25)
- Coronavirus (14)
- Critical Materials (5)
- Decarbonization (23)
- Energy Storage (38)
- Environment (53)
- Fossil Energy (1)
- Frontier (1)
- Fusion (3)
- Grid (16)
- High-Performance Computing (12)
- Hydropower (2)
- Machine Learning (11)
- Materials (22)
- Materials Science (16)
- Mathematics (3)
- Mercury (5)
- Microscopy (9)
- Molten Salt (1)
- Nanotechnology (6)
- National Security (23)
- Net Zero (4)
- Nuclear Energy (6)
- Partnerships (11)
- Physics (3)
- Polymers (6)
- Quantum Science (2)
- Renewable Energy (1)
- Security (10)
- Simulation (8)
- Summit (7)
- Transformational Challenge Reactor (3)
- Transportation (28)
Media Contacts

As vehicles gain technological capabilities, car manufacturers are using an increasing number of computers and sensors to improve situational awareness and enhance the driving experience.
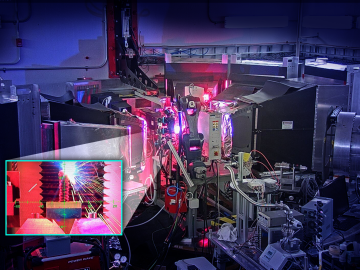
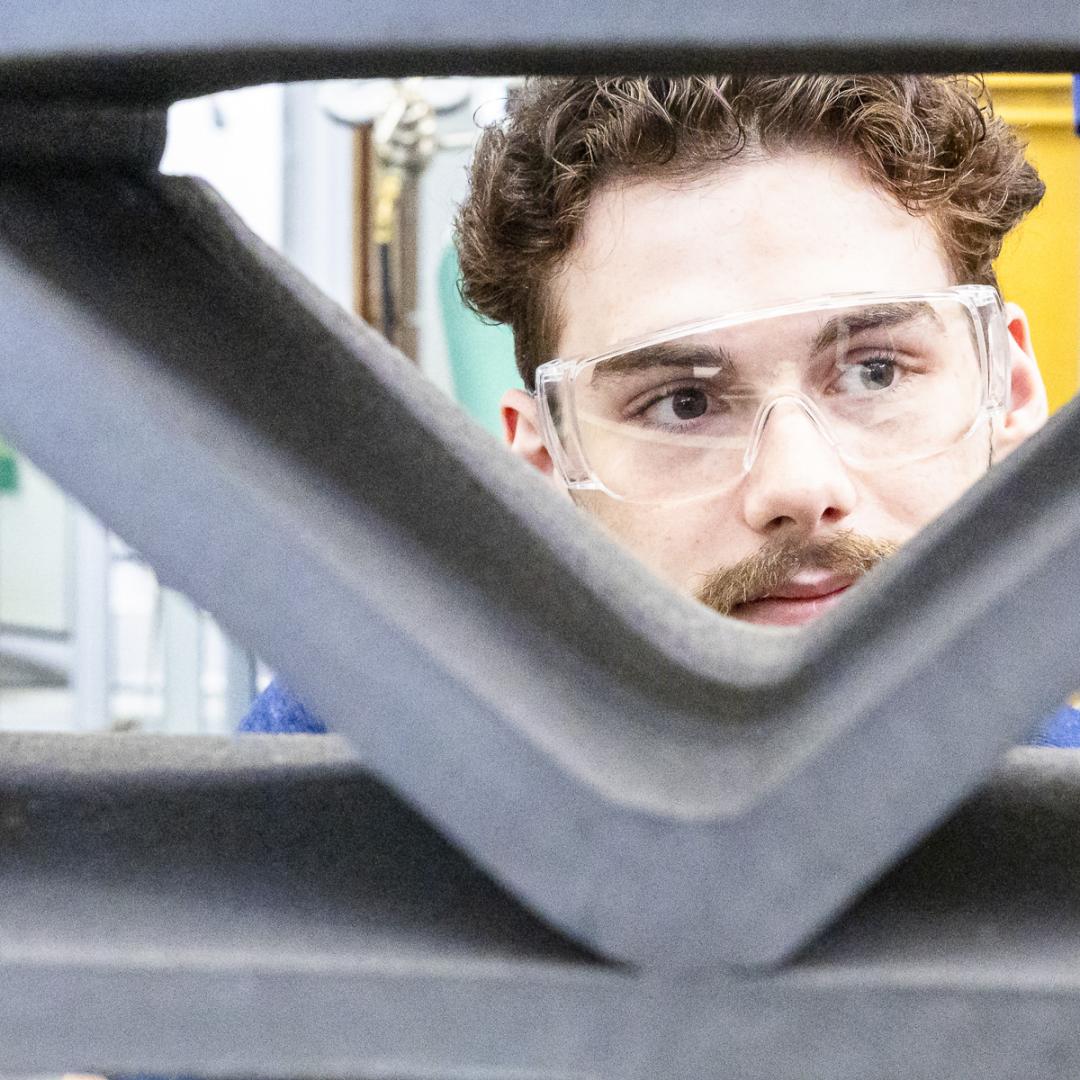
Using neutrons to see the additive manufacturing process at the atomic level, scientists have shown that they can measure strain in a material as it evolves and track how atoms move in response to stress.

Carl Dukes’ career as an adept communicator got off to a slow start: He was about 5 years old when he spoke for the first time. “I’ve been making up for lost time ever since,” joked Dukes, a technical professional at the Department of Energy’s Oak Ridge National Laboratory.

Mike Huettel is a cyber technical professional. He also recently completed the 6-month Cyber Warfare Technician course for the United States Army, where he learned technical and tactical proficiency leadership in operations throughout the cyber domain.

Mirko Musa spent his childhood zigzagging his bike along the Po River. The Po, Italy’s longest river, cuts through a lush valley of grain and vegetable fields, which look like a green and gold ocean spreading out from the river’s banks.

Growing up exploring the parklands of India where Rudyard Kipling drew inspiration for The Jungle Book left Saubhagya Rathore with a deep respect and curiosity about the natural world. He later turned that interest into a career in environmental science and engineering, and today he is working at ORNL to improve our understanding of watersheds for better climate prediction and resilience.

Like most scientists, Chengping Chai is not content with the surface of things: He wants to probe beyond to learn what’s really going on. But in his case, he is literally building a map of the world beneath, using seismic and acoustic data that reveal when and where the earth moves.

In a discovery aimed at accelerating the development of process-advantaged crops for jet biofuels, scientists at ORNL developed a capability to insert multiple genes into plants in a single step.

A technology developed at ORNL and used by the U.S. Naval Information Warfare Systems Command, or NAVWAR, to test the capabilities of commercial security tools has been licensed to cybersecurity firm Penguin Mustache to create its Evasive.ai platform. The company was founded by the technology’s creator, former ORNL scientist Jared M. Smith, and his business partner, entrepreneur Brandon Bruce.

U2opia Technology, a consortium of technology and administrative executives with extensive experience in both industry and defense, has exclusively licensed two technologies from ORNL that offer a new method for advanced cybersecurity monitoring in real time.