Filter News
Area of Research
News Topics
- (-) Advanced Reactors (1)
- (-) Clean Water (1)
- (-) Cybersecurity (5)
- (-) Physics (11)
- (-) Polymers (5)
- (-) Space Exploration (2)
- 3-D Printing/Advanced Manufacturing (6)
- Artificial Intelligence (2)
- Big Data (3)
- Bioenergy (4)
- Biology (2)
- Biomedical (4)
- Climate Change (1)
- Composites (4)
- Computer Science (20)
- Critical Materials (1)
- Energy Storage (3)
- Environment (7)
- Exascale Computing (1)
- Fusion (5)
- Grid (3)
- Isotopes (6)
- Materials Science (12)
- Mercury (2)
- Microscopy (6)
- Molten Salt (4)
- Nanotechnology (9)
- Neutron Science (10)
- Nuclear Energy (10)
- Quantum Science (3)
- Security (7)
- Summit (2)
- Transportation (9)
Media Contacts
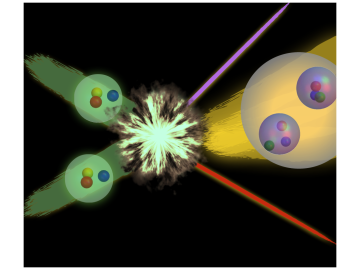
Nuclear physicists are using the nation’s most powerful supercomputer, Titan, at the Oak Ridge Leadership Computing Facility to study particle interactions important to energy production in the Sun and stars and to propel the search for new physics discoveries Direct calculatio...
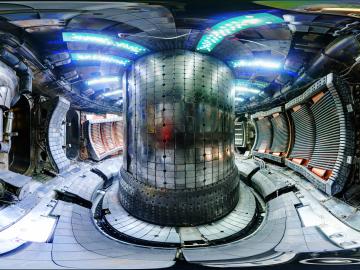
The same fusion reactions that power the sun also occur inside a tokamak, a device that uses magnetic fields to confine and control plasmas of 100-plus million degrees. Under extreme temperatures and pressure, hydrogen atoms can fuse together, creating new helium atoms and simulta...

A new Oak Ridge National Laboratory-developed method promises to protect connected and autonomous vehicles from possible network intrusion. Researchers built a prototype plug-in device designed to alert drivers of vehicle cyberattacks. The prototype is coded to learn regular timing...

After more than a year of operation at the Department of Energy’s (DOE’s) Oak Ridge National Laboratory (ORNL), the COHERENT experiment, using the world’s smallest neutrino detector, has found a big fingerprint of the elusive, electrically neutral particles that interact only weakly with matter.

Virginia-based Lenvio Inc. has exclusively licensed a cyber security technology from the Department of Energy’s Oak Ridge National Laboratory that can quickly detect malicious behavior in software not previously identified as a threat.




