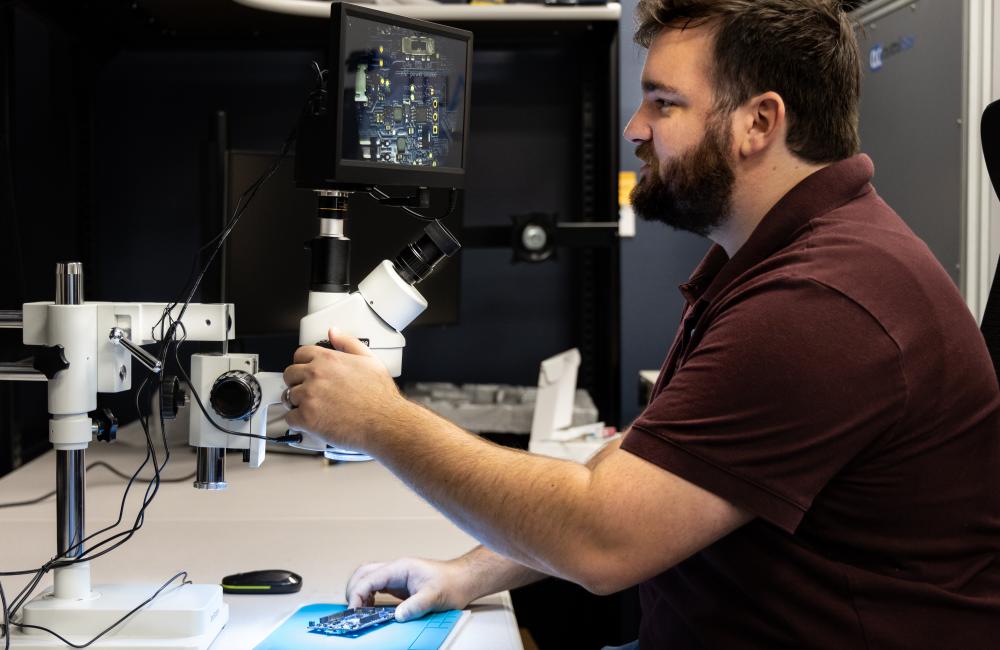
Alex Mullins, a cyber security technical professional at ORNL, deciphers microscopic markings on each chip on a board. Credit: Genevieve Martin/ORNL, U.S. Dept. of Energy
There’s a cybersecurity theory that says if nobody has easy access to a device or visibility into its software code, then they won’t be able to hack into it.
Jason Carter doesn’t buy it.
“People are persistent. They can get their hands on devices, reverse engineer code,” said Carter, who leads the Vulnerability Science Group at the Department of Energy’s Oak Ridge National Laboratory. “Ignorance of something’s vulnerabilities won’t make them go away.”
When those vulnerabilities are in the devices controlling the energy grid, the consequences could be disastrous.
Carter and his team are tackling this challenge through the Cyber Testing for Resilient Industrial Control Systems, or CyTRICS, program, a partnership among DOE, six of its national laboratories and several industrial partners to conduct supply chain assessments of critical devices used to operate the United States’ energy grid. ORNL recently delivered its first bill of materials for the DOE-wide program, enumerating all the components, subcomponents, software and firmware contained within a single device.
“We got the device from the manufacturer, took it apart piece-by-piece and looked at all the individual boards and microcomponents on those boards,” said ORNL’s Alex Mullins, a cyber security technical professional. “Then, we catalogued all the software required to operate the devices and looked through all the related files and code.”
This method, akin to a forensic investigation, creates a detailed inventory. For one relatively small device, the team documented about 180 distinct physical components and 3,500 software files, which inform more than 15,000 functions via approximately 300,000 lines of code.
The U.S. energy grid is so vast and full of hardware and software components nested within other hardware and software components that the scope of the cyber-physical security challenge is almost impossible to define. Increasingly complex, global supply chains have made it more difficult for device manufacturers to fully understand the functionality and security ramifications of every component purchased.
“Part of the CyTRICS program is figuring out exactly what it is we need to be identifying in the first place,” Carter said. “We want to know what is in the devices that are controlling the grid so we can be sure we’re not inadvertently letting adversaries into our systems.”
The program, which is funded by DOE’s Office of Cybersecurity, Energy Security, and Emergency Response, aims to enumerate and assess critical devices, developing both a holistic picture of the hardware and software functionality currently on the grid and a consolidated database for information sharing and analysis.
ORNL’s initial contribution involved designing and building internal processes and systems to catalog the information collected. It can be repetitive and mundane work, but it is essential.
“This is an incredibly time-consuming process,” Carter said. “We’re trying to mature a process that didn’t even exist a couple years ago.”
As they look to automate the process where possible, the ORNL team also hopes to conduct more vulnerability assessments related to the devices.
“We’re looking at the firmware running on these devices and determining whether an attacker can penetrate the system and cause havoc on the grid,” said Mullins.
With better understanding of those components and any associated vulnerabilities, ORNL and the CyTRICS program will help ensure the U.S. energy grid is secure and resilient against cyberattacks.
UT-Battelle manages ORNL for the Department of Energy’s Office of Science, the single largest supporter of basic research in the physical sciences in the United States. The Office of Science is working to address some of the most pressing challenges of our time. For more information, please visit energy.gov/science.